Introduction
In the world of cybersecurity, understanding basic concepts is essential before diving into advanced protection strategies. One of the most fundamental terms you will come across is “host.” If you are wondering what are hosts cybersecurity, this guide will give you a clear, practical, and beginner-friendly explanation.
A host in cybersecurity refers to any device connected to a network that can send or receive data. These devices play a critical role in communication but are also prime targets for cyberattacks. From personal laptops to enterprise servers, every host represents a potential entry point for hackers if not properly secured.
In this article, you will learn what hosts are, how they function, why they are important in cybersecurity, and how to protect them from modern threats. Whether you are a beginner or an IT professional, this guide will help you build a solid understanding.
What Is a Host in Cybersecurity?
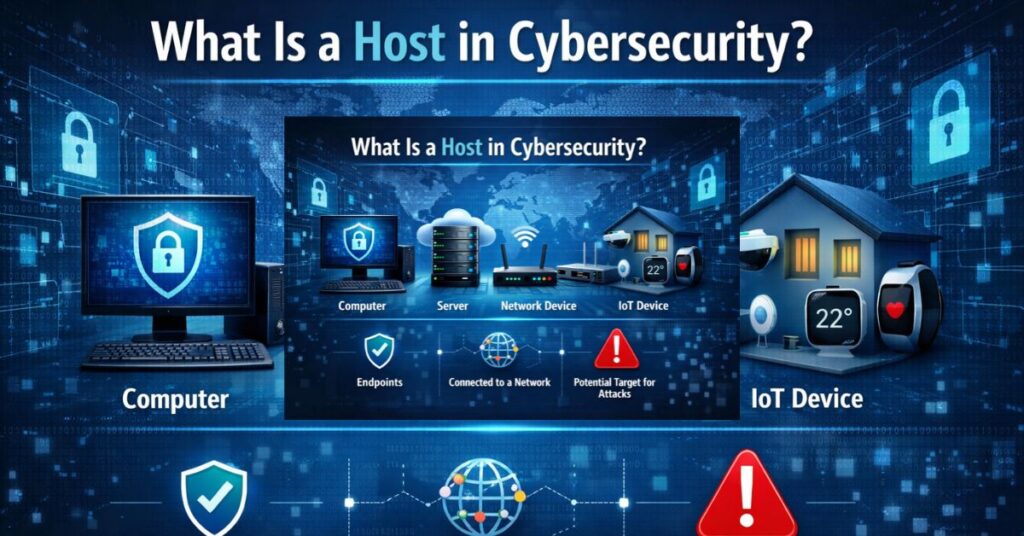
A host in cybersecurity is any device connected to a network that has its own IP address and can communicate with other devices. Hosts are the endpoints of communication in a network, meaning they send, receive, and process data.
These devices can include computers, smartphones, servers, and even IoT devices like smart cameras or thermostats. Each host plays a role in the network, whether it is serving data, requesting information, or processing tasks.
From a cybersecurity perspective, hosts are important because they are often the first target attackers try to exploit. If a hacker gains access to a host, they can potentially move deeper into the network and cause more damage.
Types of Hosts in Cybersecurity
End-User Hosts
End-user hosts are devices used by individuals, such as laptops, desktops, and smartphones. These are the most common types of hosts and are frequently targeted because users may unknowingly click on malicious links or download infected files.
Server Hosts
Server hosts provide services to other devices on the network. These include web servers, database servers, and file servers. Because they store critical data, they are highly valuable targets for attackers.
Network Devices as Hosts
Devices like routers, switches, and firewalls can also act as hosts. While their primary role is to manage network traffic, they still have IP addresses and can be targeted by cyber threats.
IoT Hosts
Internet of Things (IoT) devices are increasingly common and include smart home devices, wearable technology, and industrial sensors. These hosts often lack strong security measures, making them vulnerable to attacks.
How Hosts Function in a Network
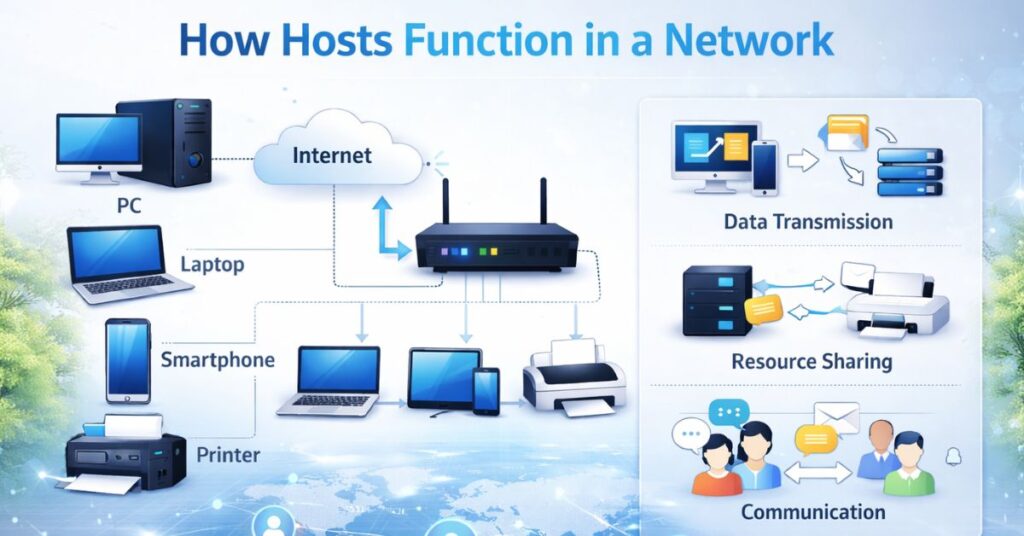
Hosts communicate with each other using network protocols such as TCP/IP. Each host is assigned a unique IP address, which allows it to send and receive data across the network.
When you visit a website, your device acts as a host that sends a request to a server host. The server processes the request and sends back the required data, such as a webpage. This entire process happens in milliseconds and involves multiple hosts interacting seamlessly.
In cybersecurity, monitoring host activity is crucial because unusual behavior can indicate a security breach. For example, if a host starts sending large amounts of data unexpectedly, it could be compromised.
Why Hosts Are Important in Cybersecurity
Hosts are critical because they are the primary points of interaction within a network. Every action, whether it is browsing the internet or accessing a company database, involves a host.
From a security standpoint, hosts are often the weakest link. Attackers exploit vulnerabilities in hosts to gain unauthorized access. Once inside, they can steal data, install malware, or disrupt operations.
Protecting hosts is therefore essential to maintaining overall network security. This is why organizations invest heavily in endpoint protection and host-based security solutions.
Common Threats to Hosts
Hosts face a wide range of cybersecurity threats, many of which are constantly evolving. Understanding these threats is the first step in protecting your systems.
Malware Attacks
Malware includes viruses, worms, ransomware, and spyware. These malicious programs can infect hosts through downloads, email attachments, or compromised websites.
Phishing Attacks
In phishing attacks, users are tricked into divulging sensitive information, such as passwords or financial information. These attacks often target end-user hosts through emails or fake websites.
Unauthorized Access
Hackers may attempt to gain access to a host by exploiting weak passwords or software vulnerabilities. Once inside, they can control the device remotely.
Insider Threats
Not all threats come from outside. Employees or authorized users can intentionally or accidentally compromise a host by misusing access privileges.
Host-Based Security Explained
Host-based security refers to the protection of individual devices within a network. Unlike network security, which focuses on protecting the entire system, host-based security focuses on each device separately.
This approach is important because even if the network is secure, a single vulnerable host can still be exploited. Host-based security includes tools and practices designed to detect, prevent, and respond to threats at the device level.
Key Components of Host-Based Security
- Antivirus and anti-malware software
- Host-based firewalls
- Intrusion detection systems (IDS)
- Encryption tools
- Access control mechanisms
These components work together to create a layered defense system that protects hosts from various threats.
Host-Based vs Network-Based Security
Understanding the difference between host-based and network-based security helps in building a comprehensive cybersecurity strategy.
| Feature | Host-Based Security | Network-Based Security |
| Focus | Individual devices | Entire network |
| Protection Level | Endpoint-level | Network-wide |
| Tools | Antivirus, firewall | IDS, IPS, firewalls |
| Flexibility | High | Moderate |
| Risk Coverage | Device-specific | Broad threats |
Both approaches are important and should be used together for maximum protection.
Best Practices to Secure Hosts
Protecting hosts requires a combination of tools, policies, and user awareness. Here are some proven best practices to improve host security.
Keep Software Updated
Regular updates ensure that known vulnerabilities are patched. Attackers often gain access through outdated software.
Use Strong Passwords
Hackers can easily access sensitive information with weak passwords. When possible, use complex passwords and enable multi-factor authentication.
Install Security Software
Reliable antivirus and firewall solutions provide a strong first line of defense against malware and unauthorized access.
Limit User Access
Not every user needs full access to a system. Limiting permissions reduces the risk of accidental or intentional misuse.
Monitor Host Activity
Continuous monitoring helps detect unusual behavior early. This allows for quick response before significant damage occurs.
Real-World Example of Host Security
Consider a company where employees use laptops connected to a corporate network. Each laptop is a host. If one employee downloads a malicious file, the laptop can become infected.
Without proper security measures, the malware could spread to other hosts in the network. However, with host-based security in place, the threat can be detected and isolated before it spreads.
This example highlights why securing individual hosts is just as important as protecting the entire network.
Future of Host Security in Cybersecurity
As technology evolves, so do cyber threats. The rise of remote work, cloud computing, and IoT devices has increased the number of hosts in networks.
Modern cybersecurity strategies now focus on advanced solutions such as:
- Endpoint Detection and Response (EDR)
- Artificial Intelligence-based threat detection
- Zero Trust security models
These innovations aim to provide stronger protection by continuously monitoring and analyzing host activity.
Conclusion
Understanding what are hosts cybersecurity is essential for anyone interested in protecting digital systems. Hosts are the backbone of network communication, but they are also the most targeted components in cyberattacks.
By recognizing the types of hosts, understanding common threats, and implementing strong security practices, you can significantly reduce risks. Whether you are managing a personal device or an enterprise network, securing hosts should always be a top priority.
In today’s digital world, strong host security is not optional it is a necessity.
A host is any device connected to a network that can send or receive data, such as a computer, smartphone, or server.
Hosts are important because they are common targets for cyberattacks. Securing them helps protect the entire network.
Host-based security focuses on protecting individual devices using tools like antivirus software, firewalls, and monitoring systems.
Examples include laptops, desktops, servers, smartphones, and IoT devices like smart home systems.
You can protect your host by updating software, using strong passwords, installing security tools, and monitoring activity regularly.
Ali is an SEO specialist and technology content writer at Techsprinto, covering AI tools, SEO software, and blogging resources. He creates practical reviews and guides to help creators and marketers choose the right digital tools.


1 thought on “What Are Hosts in Cybersecurity? (Complete Guide)”